How Cybercriminals Operate and Make Money
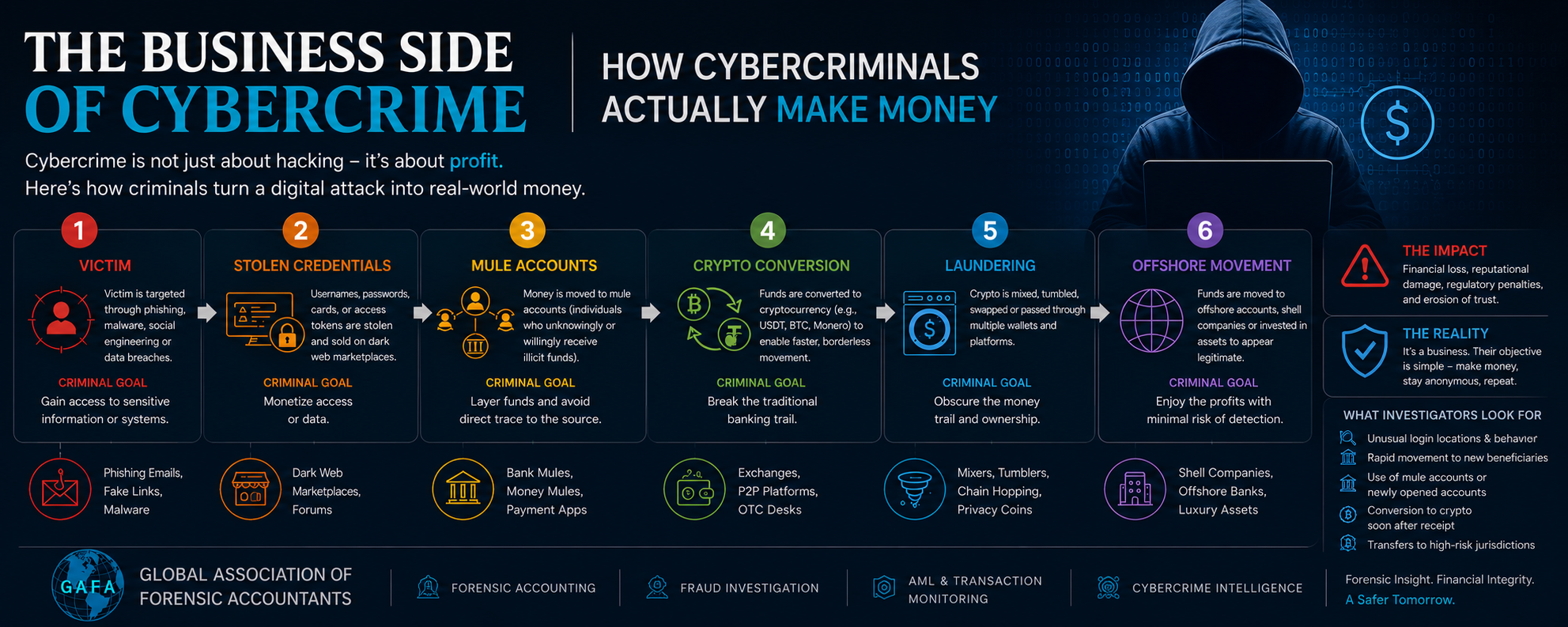
When people hear the term cybercrime, they often imagine hackers sitting behind screens, breaking into systems or stealing passwords. While that image is not entirely incorrect, it only explains one small part of a much larger ecosystem. Modern cybercrime is driven by financial gain. Behind almost every major cyberattack, there is a carefully planned monetization strategy, which is designed to convert the digital access into real profit.
Lets understand the business side of frauds.
The Rise of the “Crime-as-a-Service” Economy
Modern cybercrime is no longer driven by isolated hackers working alone from dark rooms. It has evolved into a highly organized underground business ecosystem that closely resembles legitimate corporate structures. In many ways, today’s cybercriminal networks operate with the same commercial logic used by genuine businesses:
Specialization
Scalability
Outsourcing
Automation
Branding
customer service
and profit optimization.
This transformation is often described as the rise of the “Crime-as-a-Service” model.
Business Model- Crime-as-a-Service
Today’s cybercriminal ecosystem operates very much like a legitimate business industry. In fact, the rise of “Crime-as-a-Service” has transformed cybercrime into a structured commercial model where criminals offer specialized services to one another, similar to how modern companies outsource expertise.
Delegation of Responsibilities-Criminals uses focus groups. Some focus only on phishing campaigns and social engineering operations wherein others specialize in malware development, ransomware deployment, stolen credential sales, mule account management, cryptocurrency conversion, or money laundering networks.
Criminal Market Place– In many dark web forums, cybercrime functions almost like an e-commerce platform. There are criminal marketplaces that provide customer support, subscription-based hacking tools, and profit-sharing arrangements.
Sellers advertise their “services,” provide user reviews, offer subscription packages, and maintain reputational ratings to attract more buyers. Some ransomware groups even provide technical support portals to victims in order to facilitate ransom payments more efficiently. Ironically, certain criminal operations demonstrate better customer responsiveness than genuine businesses.
Departmentalization -Just as legitimate organizations have separate departments for sales, finance, logistics, technology, and customer management , the cybercriminal networks also divide responsibilities to maximize efficiency, scalability, and profit.One actor may steal data, another may monetize it, while another launders the proceeds through layered financial channels. The attack itself is often only the starting point.
Outsourcing – like the legitimate companies outsource payroll processing, cloud infrastructure, marketing, or logistics, cybercriminal organizations now outsource different components of criminal operations to specialized actors. One group may focus entirely on phishing campaigns designed to steal credentials. Another may develop ransomware tools and lease them to affiliates in exchange for a percentage of profits.Some actors specialize in credential harvesting, while others operate mule account networks or cryptocurrency laundering services.
Franchise Model– The financial structure of these networks also mirrors legitimate commercial models. Some cybercriminal groups operate on commission-sharing arrangements similar to franchise businesses.In ransomware-as-a-service operations, developers create and maintain the ransomware infrastructure while affiliates carry out attacks. Profits are then distributed between the parties according to predefined percentages. This significantly lowers the entry barrier into cybercrime because individuals no longer need deep technical capabilities to participate.
Innovation- Cybercriminals constantly innovate because innovation increases profitability. They study market trends, exploit emerging technologies, and adapt quickly to new security controls. Artificial intelligence, deepfake technology, automated phishing kits, and synthetic identity fraud are increasingly becoming part of this underground economy. Criminal groups understand that speed, scale, and automation directly improve financial returns.
High Internal Controls- Many cybercriminal organizations maintain strict operational security practices. Internal communication channels are encrypted. Access to criminal marketplaces may require vetting or sponsorship. Some groups prohibit attacks against specific countries to avoid attracting local law enforcement attention. Others maintain internal codes of conduct and disciplinary systems. This level of organization demonstrates how far cybercrime has evolved from opportunistic hacking into structured financial enterprise.
The specialization within these criminal ecosystems increases operational efficiency.
One group focuses on acquiring access.
Another focuses on monetization.
Another handles money laundering and offshore movement.
This compartmentalization reduces direct exposure and makes investigations significantly more difficult because multiple independent actors may operate across different jurisdictions.
For example, a phishing email targeting a finance executive in India may be designed by one criminal group, hosted through infrastructure located in Eastern Europe, executed through compromised servers in another country, monetized through mule accounts in Southeast Asia, and eventually laundered through cryptocurrency wallets linked to offshore entities. The crime itself becomes globally distributed.
The business objective behind these operations is remarkably similar to legitimate enterprises: maximize revenue while minimizing operational risk.
Perhaps the most important reality is that cybercrime today is fundamentally profit-driven. The attack itself is often secondary. The real focus lies in monetizing stolen access, moving illicit funds through layered channels, obscuring transaction trails, and integrating proceeds into the financial system without detection.
This is precisely why cybercrime investigations increasingly require expertise beyond traditional cybersecurity. Understanding malware alone is no longer sufficient. Investigators must understand financial flows, shell company structures, cryptocurrency tracing, trade-based laundering methods, mule account behavior, and cross-border transaction patterns.
The future of financial crime investigation will belong to professionals who understand both the technical mechanics of attacks and the economics behind them.
Because modern cybercriminals are not simply hackers anymore.
They are organized financial operators running illegal digital businesses.
Global Association of Forensic Accountants (GAFA) Advancing professional knowledge in forensic accounting, fraud investigation, cybercrime intelligence, and anti-money laundering
.